Assessment Evaluation and Standardization Program

CPGs & HVA 3.0 Courses Now Available
The Cybersecurity Performance Goals (CPGs) and High Value Asset 3.0 (HVA 3.0) Assessment training courses are now live on CISA Learning. Help CISA defend the nation's critical infrastructure by logging on to CISA Learning and starting your cyber assessor journey today
The mission of CISA's Assessment Evaluation and Standardization (AES) program is to increase the quality and quantity of cyber professionals who can execute cyber assessments independently according to CISA’s standards and methods.
Training assessors to conduct CISA standard Cyber Risk Assessments is a major step in establishing an ecosystem to provide national-level visibility and drive initiatives to reduce risk.
Participants who receive their AES training course certificate can execute assessments according to CISA standards; however, only CISA personnel are authorized to conduct official CISA assessments.
- How does AES complete its mission?
The AES program accomplishes its mission by:
- Producing a federal and private sector workforce of prepared and qualified assessors.
- Ensuring assessors have the knowledge and skills necessary to conduct assessments according to the CISA standards and methodologies.
- Providing a framework to help assure assessment results are high quality, consistent, and repeatable.
- Why is AES important?
The AES program is important for the following reasons:
- AES is the only supporting resource for the non-Tier 1 High Value Assets 3.0 (HVA 3.0) communities in meeting the Office of Management and Budget (OMB) mandate for required conduct of required assessments every three-years.
- AES is the only CISA-assessment methodology training resource for Federal Civilian Executive Branch (FCEB), Federal Department and Agencies (D/A), National Guard, State, Local, Tribal, and Territorial (SLTT), and Critical Infrastructure (CI).
- AES is authorized to train all manner of domestic entities on Cyber Security Assessments to support Federal (and in some cases SLTT) self-assessments.
- Who is the audience for the AES program?
The approach aims to assist all government and critical infrastructure to include SLTT, public, and private sector Organizations.
Audience
- Federal Civilian Executive Branch (FCEB)
- Federal Department and Agencies (D/A)
- National Guard (.MIL)
- State, Local, Tribal, and Territorial (SLTT)
- Critical Infrastructure (CI)
- Domestic Public and Private entities
- What role will I be eligible for upon completing the AES courses?
Assessment Lead (AL)
- Serves as the primary assessment team point of contact (POC).
- Leads the assessment team.
- Manages the overall assessment execution.
- Debriefs and delivers the assessment report.
- Role for the following assessments:
- Cybersecurity Performance Goals (CPG)
- High Value Assets 3.0 (HVA 3.0)
- Validated Architecture Design Review (VADR)
Technical Lead (TL)
- Responsible for overall assessment execution.
- Leads the Technical Exchange Meeting (TEM).
- Writes the majority of the assessment report.
- Supports meetings throughout the assessment.
- Role in HVA 3.0 assessments.
Operator (OP)
- Leads the Penetration Test.
- Responsible for the testing results appendix of the assessment report; contributes to other portions.
- Supports meetings throughout the assessment.
- Must pass an additional pre-course exam (OST) for acceptance into the course.
- Role in Risk and Vulnerability Assessment (RVA) assessments.
- When will the courses be available on the new Learning Management System (LMS)?
Available Now:
- Cybersecurity Performance Goals (CPGs)
- High Value Assets 3.0 (HVA 3.0)
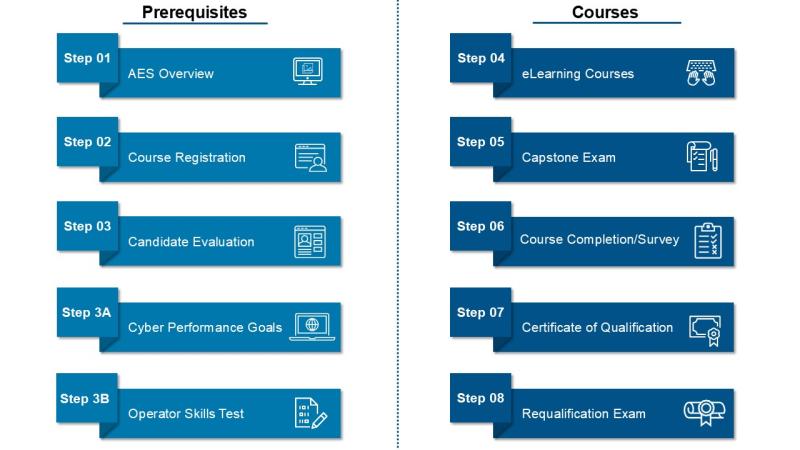
AES Assessment Training Process
Each student in the AES assessment program will follow the steps below based on AES role and course to become an AES qualified assessor.
AES Overview Video
The Assessment Evaluation and Standardization (AES) Program qualifies individuals to conduct Cybersecurity and Infrastructure Security Agency (CISA) cyber assessments.
AES Training Courses
Interested in taking AES courses? Let us know which courses you are interested in by joining the AES Roster, so you can stay updated on when those courses will be available.

Cybersecurity Performance Goals (CPGs) Course
Evaluates whether a minimum baseline of cybersecurity technologies and practices are implemented in Information Technology (IT) and Operational Technology (OT) environments in small- and medium-sized organizations.
Available Now

Cybersecurity Evaluation Tool (CSET®) Course
Provides an overview of CSET® helping users navigate and utilize key features to successfully perform assessments and evaluate an organization's security posture in a systematic, disciplined, and repeatable manner.

High Value Assets 3.0 (HVA 3.0) Course
Evaluates the HVA security architecture to identify potential risks from technical concerns using HVA 3.0 methodology.
Available Now

Risk and Vulnerability Assessment (RVA) Course
Evaluates on-site data and national threats and vulnerabilities to identify potential exploitation of network security controls.

Validated Architecture Design Review (VADR) Course
Evaluates systems, networks, and security services to determine their reliability and resiliency of design, construction, and operation.
Browse Featured AES Resources

AES Fact Sheet
The AES Program qualifies individuals to conduct CISA assessments in the active engagement of securing the nation's physical and cyber infrastructure against threats.

AES Program Overview
Overview of the AES program's training process, qualification process, and assessments.

AES Code of Ethics and Compliance
This document describes CISA’s expectations of students participating in AES program courses.

AES Assessment Roles
Overview of each AES assessment role: Assessment Lead, Technical Lead, Operator, and Sector-Specific Subject Matter Expert.

AES HVA Qualification Policy
This document describes CISA’s policy for becoming a qualified AES HVA assessor.

Downloading and Installing CSET
The Cyber Security Evaluation Tool (CSET) provides a systematic, disciplined, and repeatable approach for evaluating an organization’s security posture.
Contact
To ask a question or provide other feedback on AES training, contact us at aestraining@mail.cisa.dhs.gov




