Archived Content
In an effort to keep CISA.gov current, the archive contains outdated information that may not reflect current policy or programs.
Secure Our World
Simple ways to protect yourself, your family and your business from online threats.
Staying Safe Online is Easier Than You Think
Every day we are more and more connected—whether messaging family and friends, shopping online or ordering supplies for our small businesses. It’s important to take steps to stay safe when using our phones, laptops and smart devices. We can Secure Our World by taking simple actions each day when connected.
Learn More About the Four Easy Ways to Stay Safe Online
Online criminals look for easy targets, like people who don’t take basic precautions. If we take the following four steps, we won’t be as vulnerable to their deceptive tactics. It will be much harder to scam us or steal our information. Let’s start now.

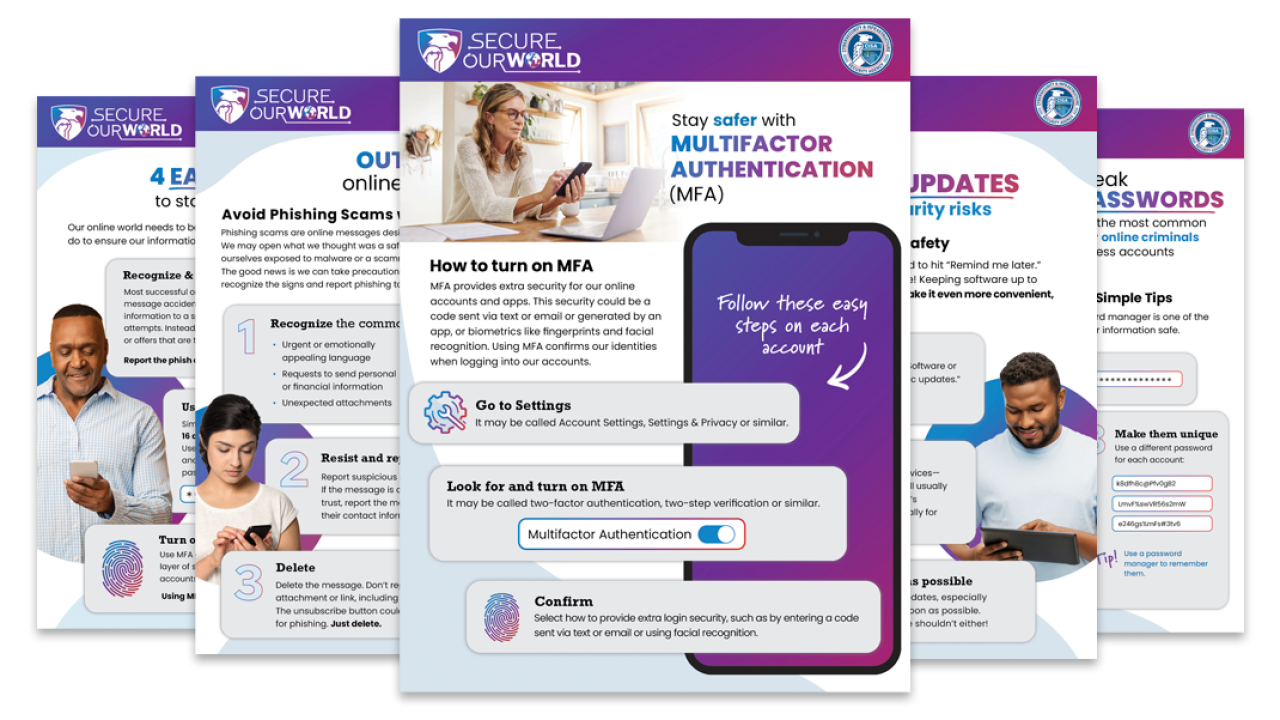
Recognize & Report Phishing
Phishing often tries to get us to open a harmful attachment or share personal information. Learn what to look for to avoid the "phish hook."

Use Strong Passwords
Using strong passwords and a password manager are some easy ways to protect ourselves from someone logging into an account and stealing data or money.

Turn on MFA
Multifactor authentication means using more than a password to access an app or account. With MFA, we might be asked to enter a text code or use a fingerprint. It makes us much safer from someone accessing our accounts.

Update Software
Don't delay software updates. Flaws in software can give criminals access to files or accounts. Programmers fix these flaws as soon as they can, but we must install updates for the latest protection!
Become a Secure Our World Partner
Help CISA increase the security of our nation by partnering with our Secure Our World program. Explore our resources and learn more about how to partner with us.
Secure Our World: Simple Steps to Protect Your Family
Secure Our World: Simple Steps to Protect Your Family | Audio Description
Secure Our World Resources
Learn more about the four ways to stay safe online with Secure Our World Tip Sheets, translated in various languages, and other resources.

Secure Our World Videos
Watch our videos to learn how to stay safe online.
Related Content

Secure Yourself & Your Family
Quick steps we can all take to greatly increase our safety and protect our money, identity, data and more.

Secure Your Business
Prevent malicious threats that could cause hassle, financial losses or even business closure. Protect your business, employees and customers!

Secure Your Products
Adopt Secure by Design practices for your products that reasonably protect against malicious actors and put customer safety first.

Cybersecurity Guidance and Resources for High-Risk Communities
Digital security tools and tips for civil society organizations and other communities at heightened risk of being targeted by advanced cyber threat actors.








